Muistiinpano
Tämän sivun käyttö edellyttää valtuutusta. Voit yrittää kirjautua sisään tai vaihtaa hakemistoa.
Tämän sivun käyttö edellyttää valtuutusta. Voit yrittää vaihtaa hakemistoa.
This page introduces tools to secure network access between the compute resources in the Azure Databricks serverless compute plane and customer resources. To learn more about the control plane and the serverless compute plane, see Networking security architecture.
To learn more about classic compute and serverless compute, see Compute.
Note
Azure Databricks charges for networking costs when serverless workloads connect to customer resources. See Understand Databricks serverless networking costs.
Serverless compute plane networking overview
Serverless compute resources run in the serverless compute plane, which is managed by Azure Databricks. Account admins can configure secure connectivity between the serverless compute plane and their resources. This network connection is labeled as 2 on the diagram below:
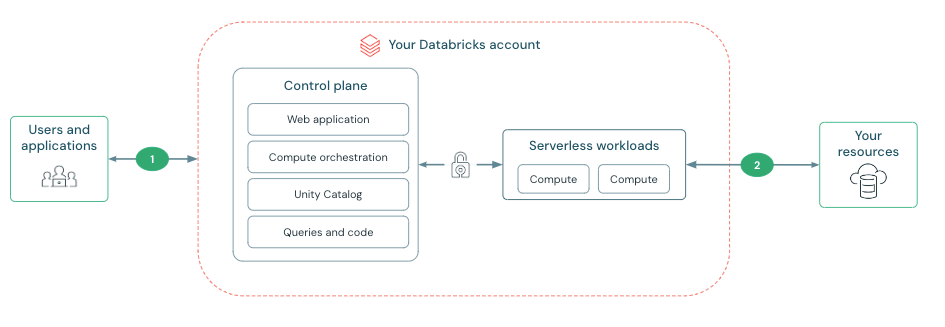
Connectivity between the control plane and the serverless compute plane is always over the cloud network backbone and not the public internet. For more information on configuring security features on the other network connections in the diagram, see Networking.
What is a network connectivity configuration (NCC)?
Serverless network connectivity is managed with network connectivity configurations (NCCs). NCCs are account-level regional constructs that manage private endpoint creation.
Important
By June 9, 2026, any existing Azure storage account that allowlists Azure Databricks serverless subnet IDs must be onboarded to a network security perimeter and must allowlist the AzureDatabricksServerless service tag. See Configure an Azure network security perimeter for Azure resources.
Account admins create NCCs in the account console. An NCC can be attached to one or more workspaces to manage access from serverless compute to your Azure resources.
When you add a private endpoint to an NCC, Azure Databricks creates a private endpoint request to your Azure resource. After you accept the request, Azure Databricks uses the private endpoint to access your Azure resource from the serverless compute plane. See Configure private connectivity to Azure resources.
If no private endpoint is configured, serverless compute connects to Azure storage using service endpoints and to other resources using NAT IPs. You can identify traffic from Azure Databricks service endpoints to your storage using the AzureDatabricksServerless service tag, which can be scoped to your region (for example, AzureDatabricksServerless.EastUS2). To use this tag, onboard your storage account to a network security perimeter. See Configure an Azure network security perimeter for Azure resources.
Note
Azure Databricks uses service endpoints, private IPs, and public IPs to connect to resources based on their location and type. These connectivity methods are generally available unless explicitly stated otherwise.